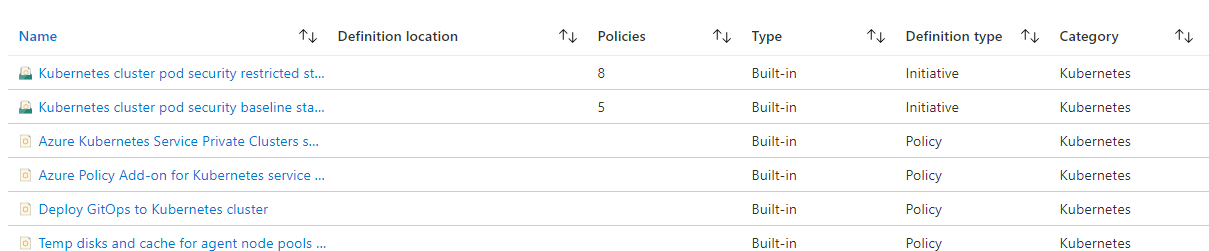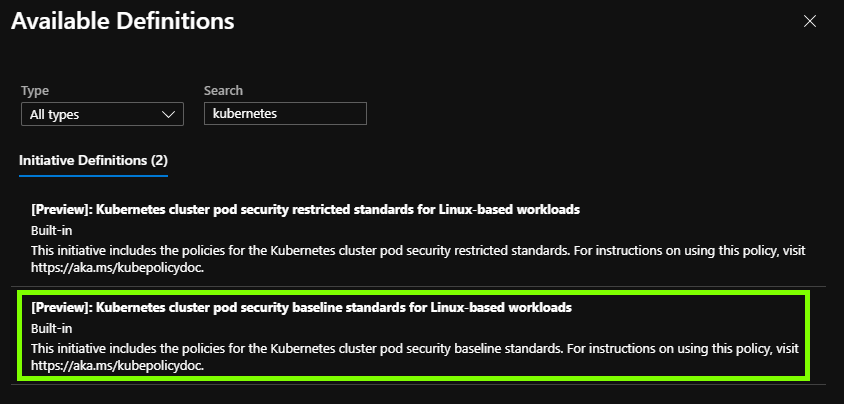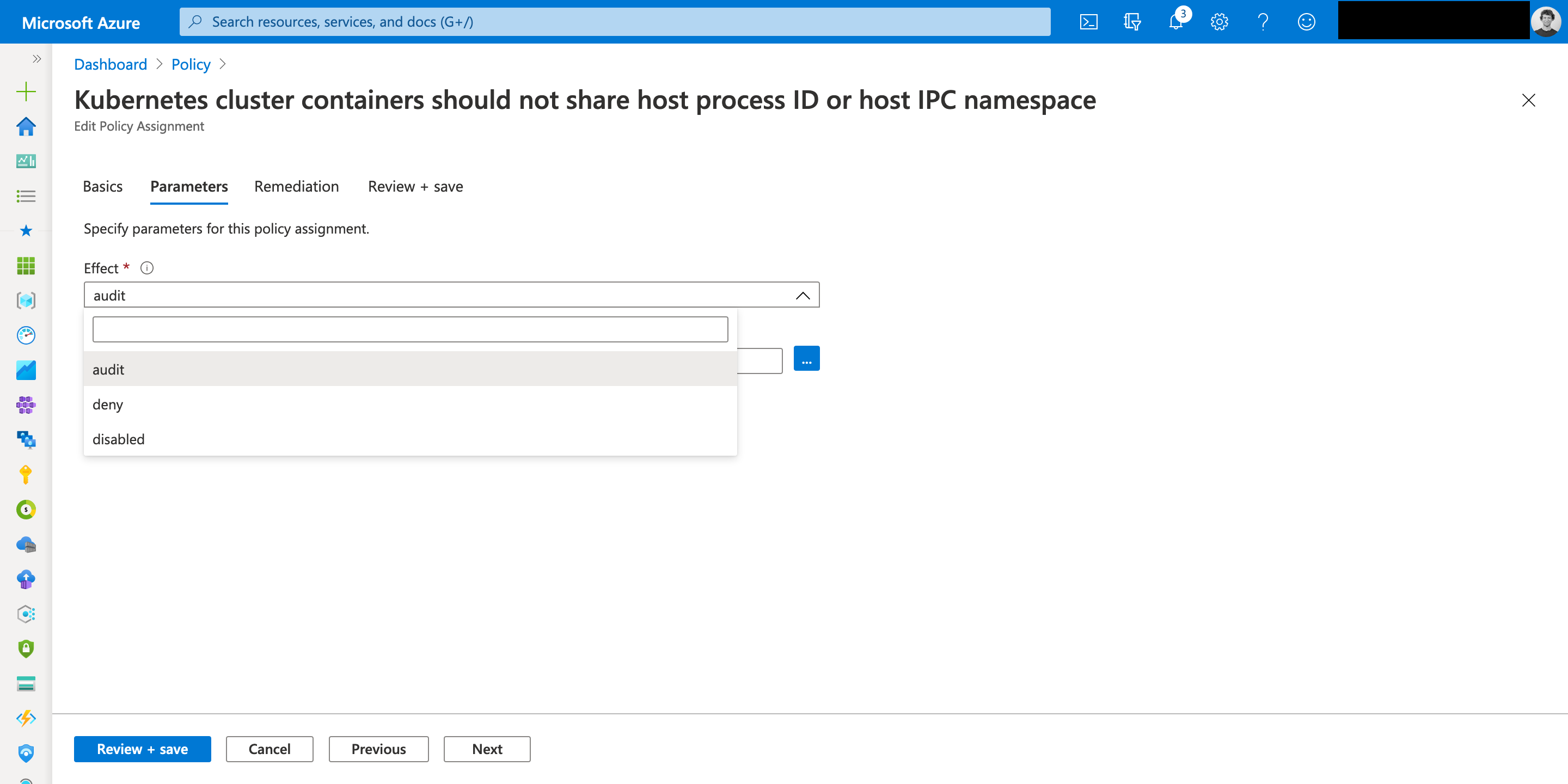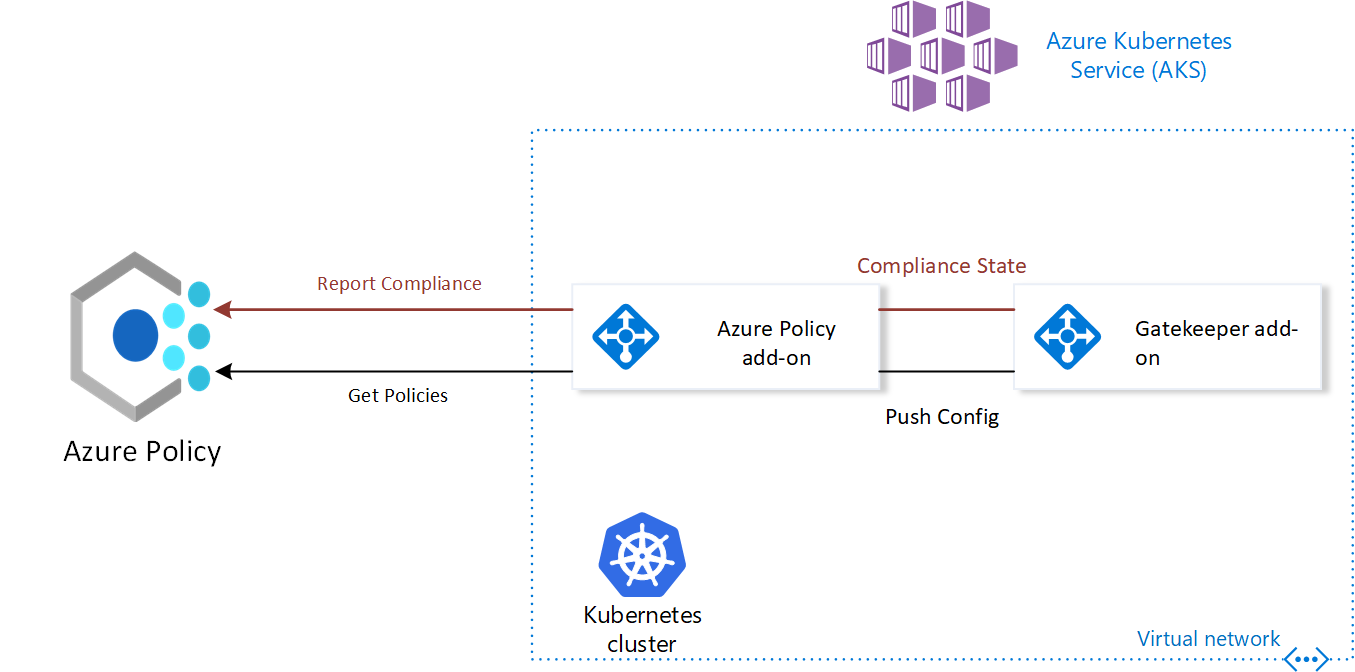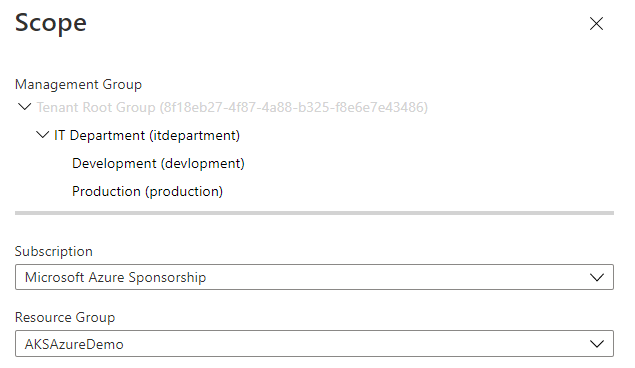
Azure Spring Clean: Replacing Kubernetes Pod Security Policies with Azure Policy on AKS - samcogan.com

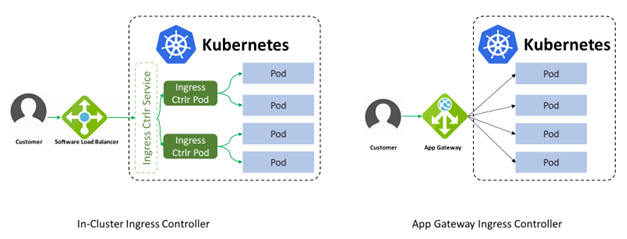
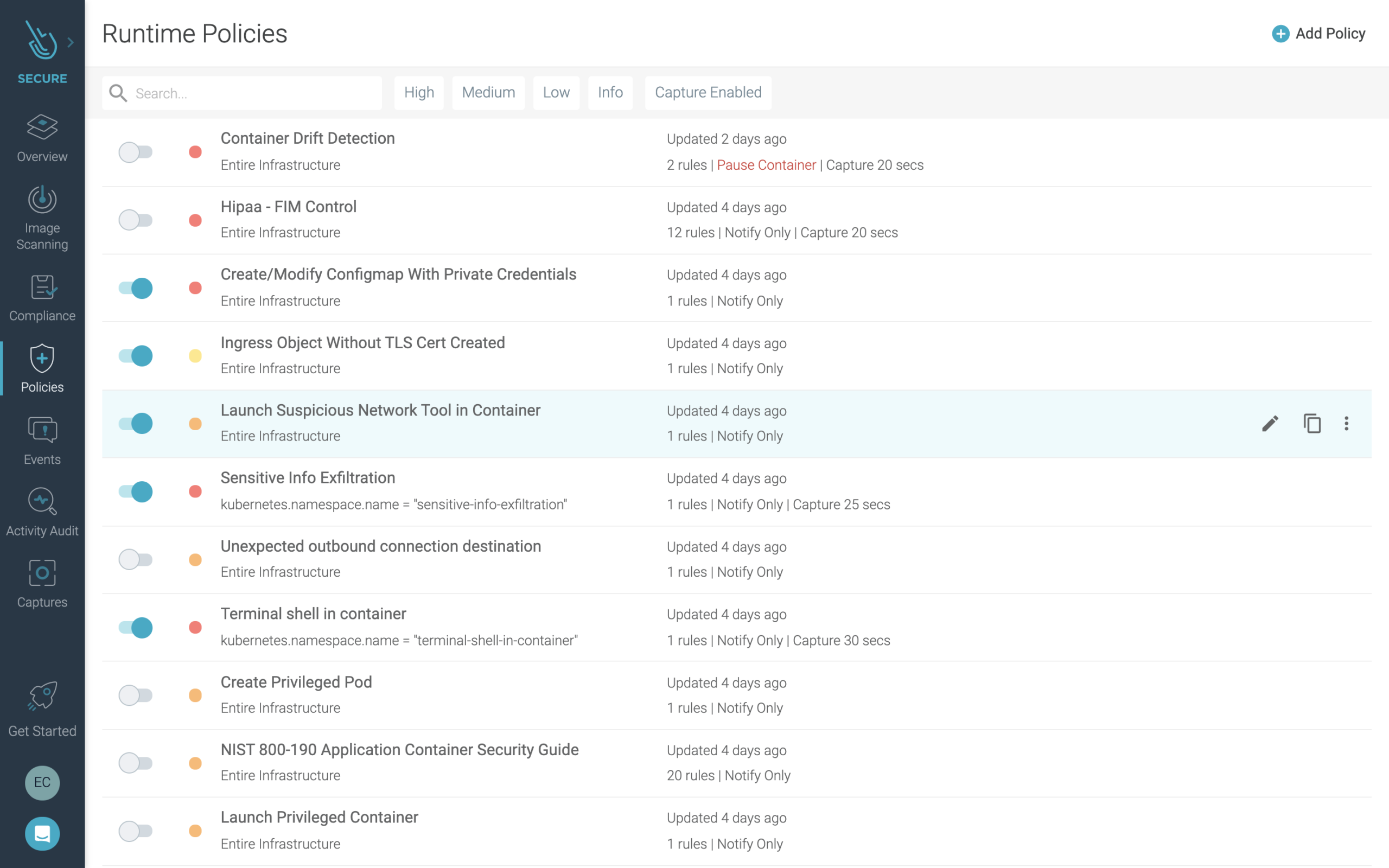
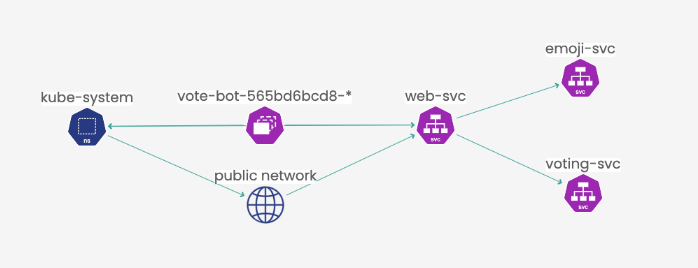
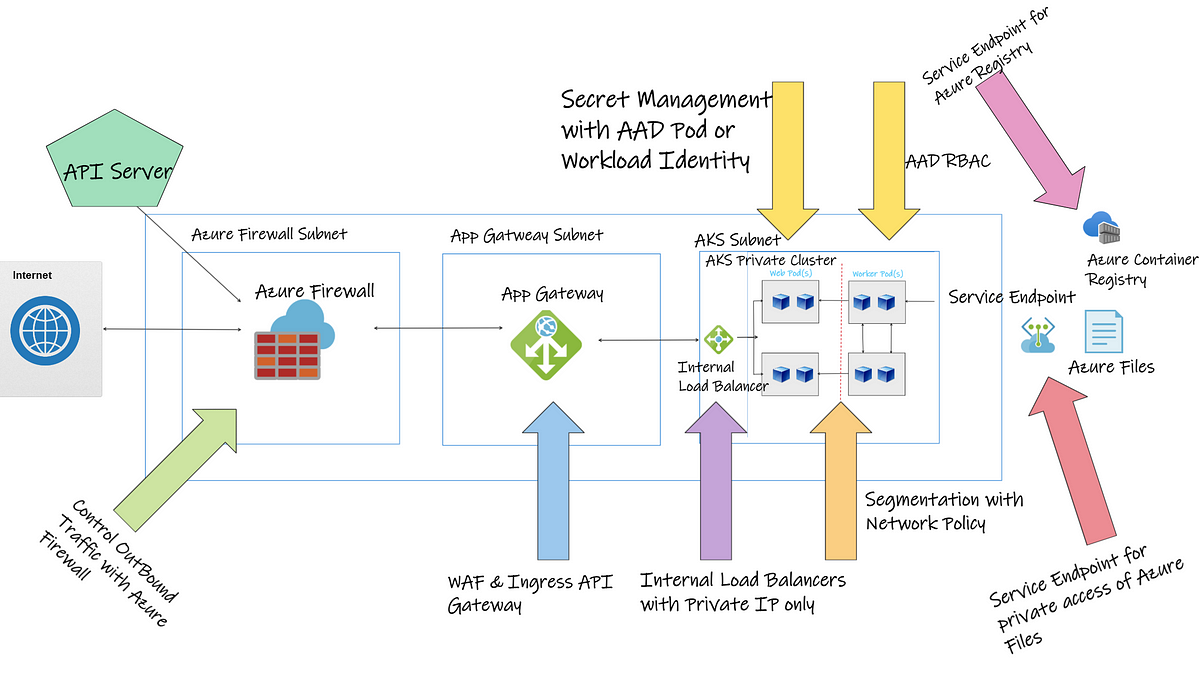
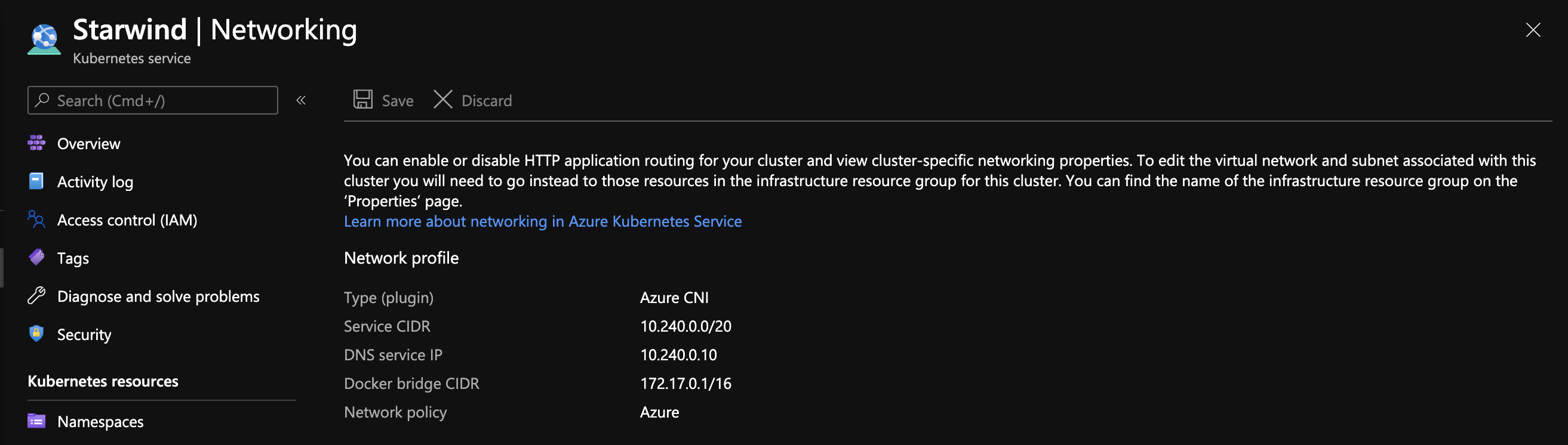
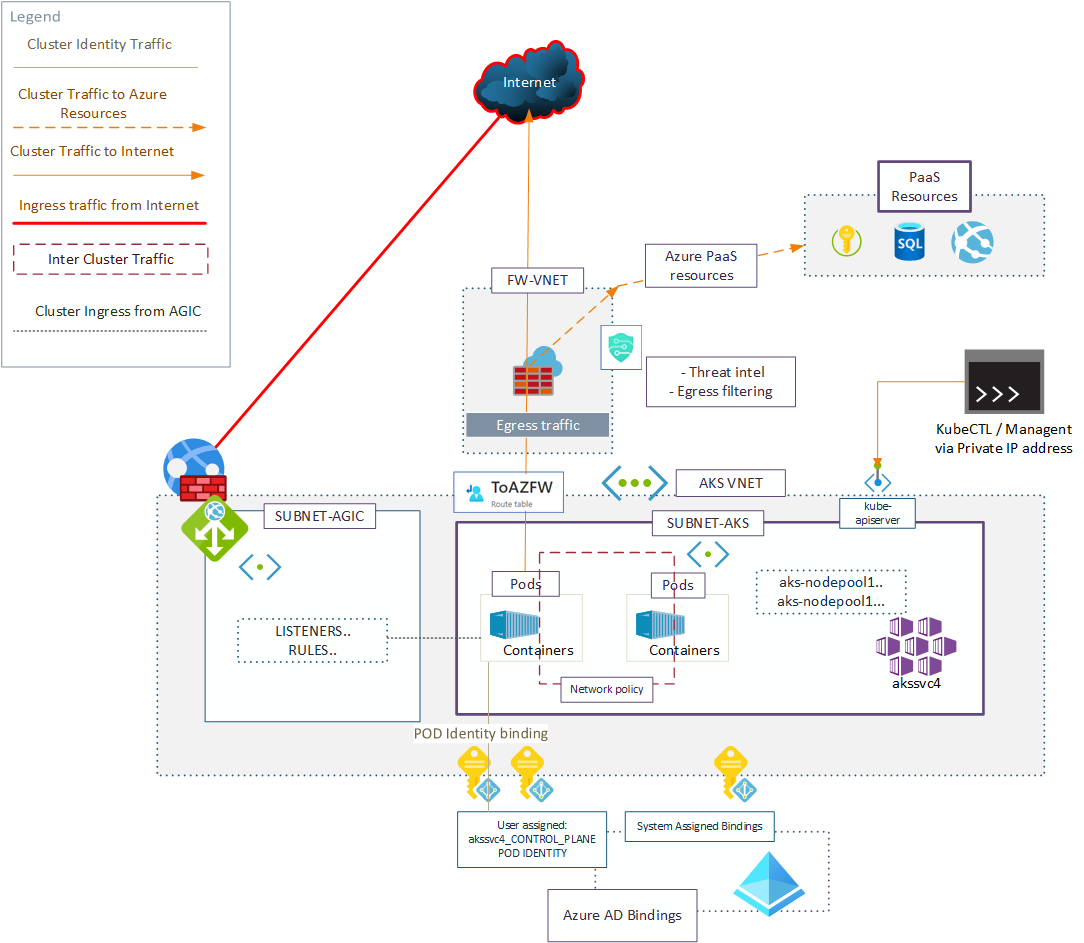
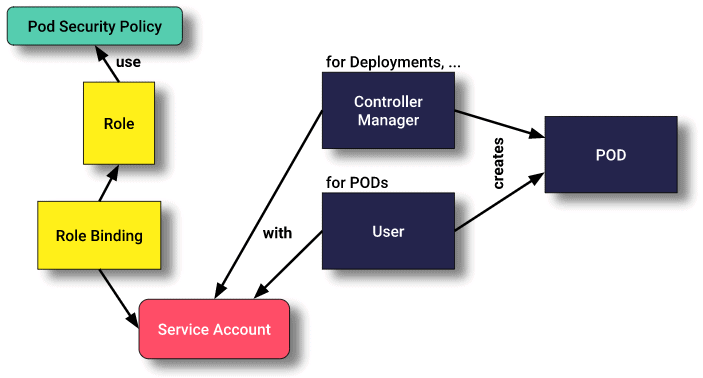
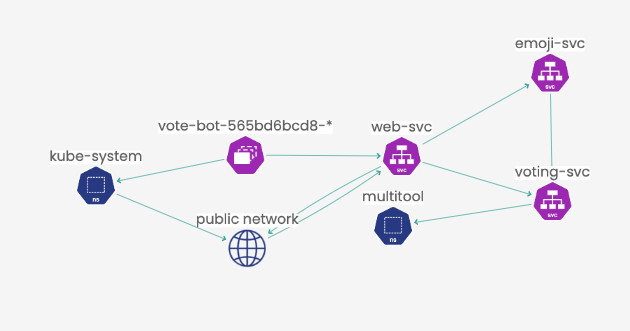
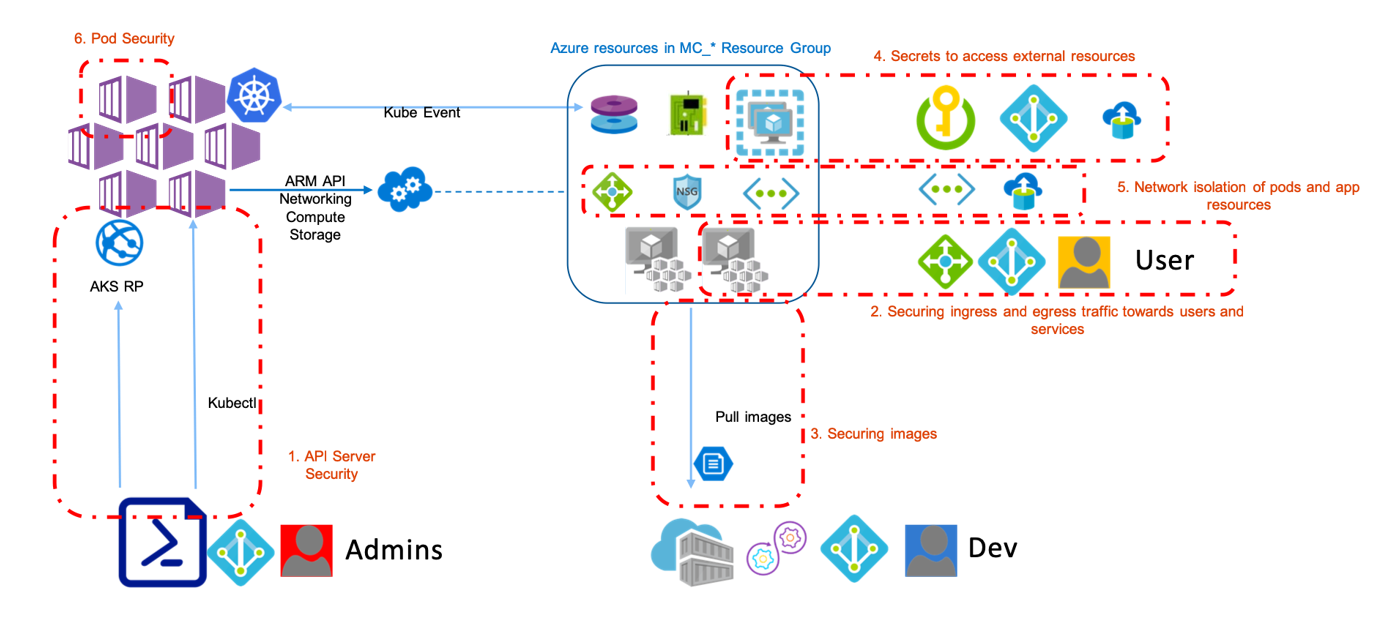
Azure Kubernetes Services (AKS). How to secure your AKS cluster after Pod Security Policy removal - sysadminas.eu

Developer best practices - Pod security in Azure Kubernetes Services (AKS) - Azure Kubernetes Service | Microsoft Learn