Enhancing Data Security with an Effective IT Security Policy | by Security Enthusiast | AVM Consulting Blog | Medium
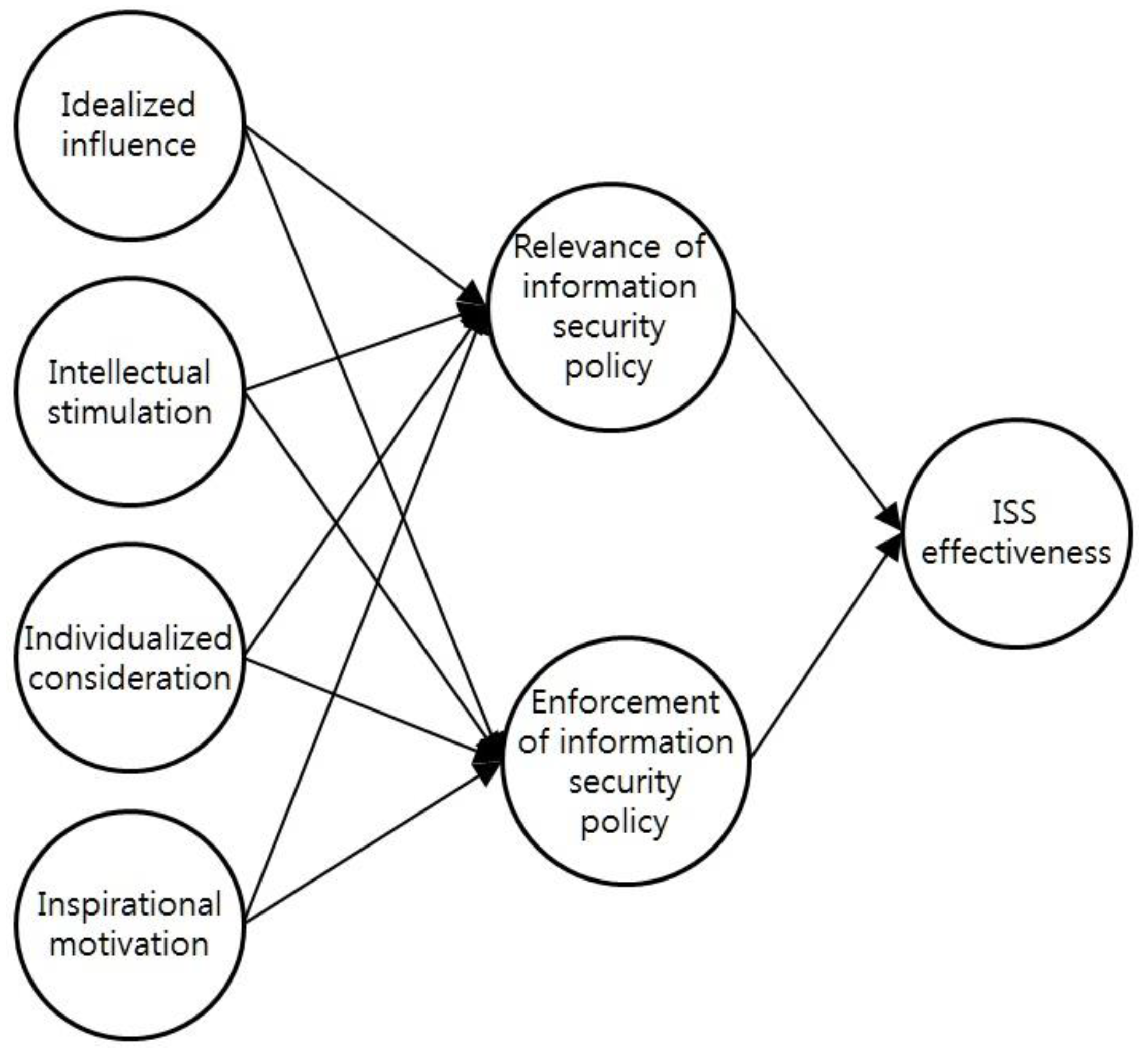
Sustainability | Free Full-Text | Leadership of Information Security Manager on the Effectiveness of Information Systems Security for Secure Sustainable Computing

Security Policies and Implementation Issues (Information Systems Security & Assurance): 9781284199840: Computer Science Books @ Amazon.com
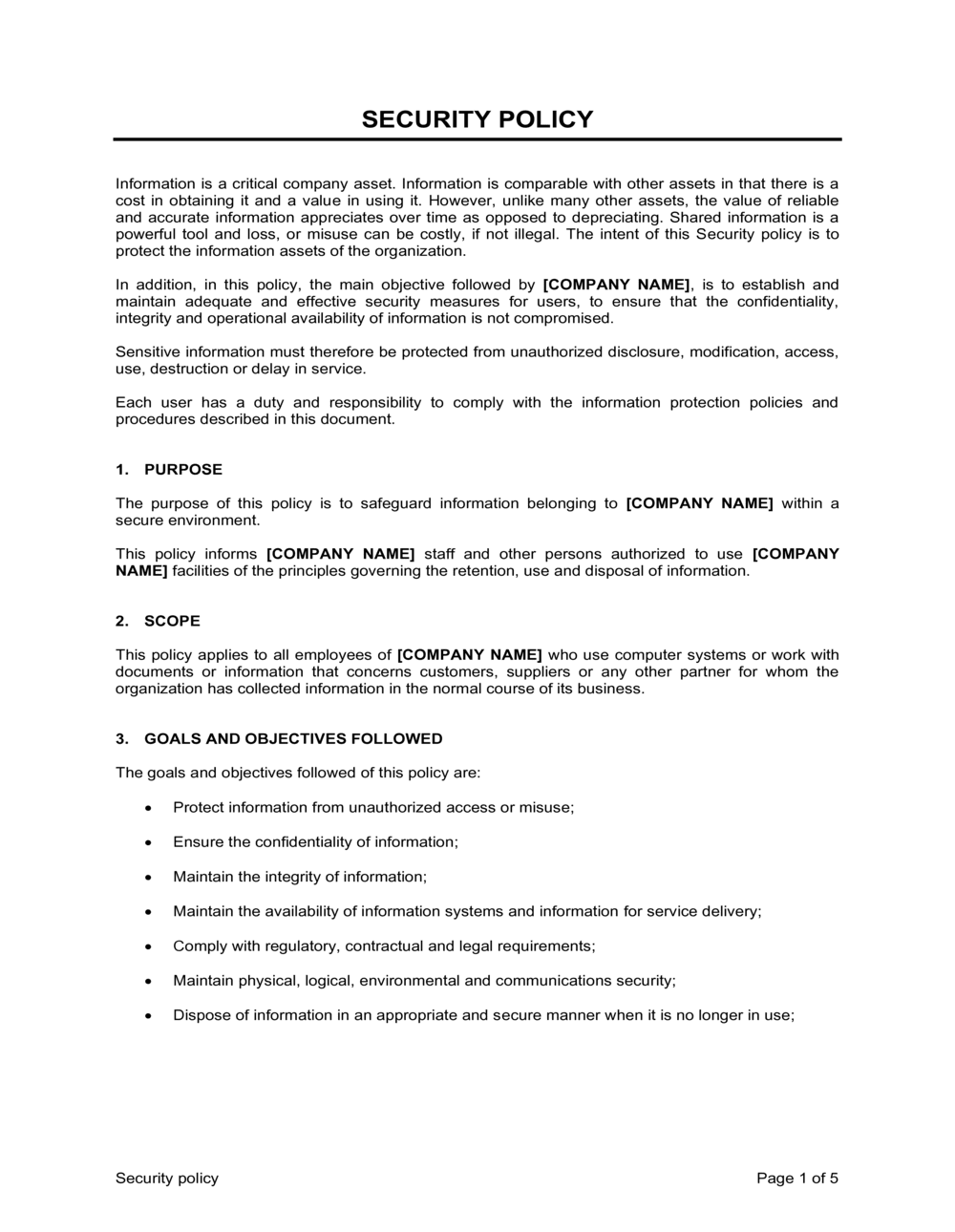
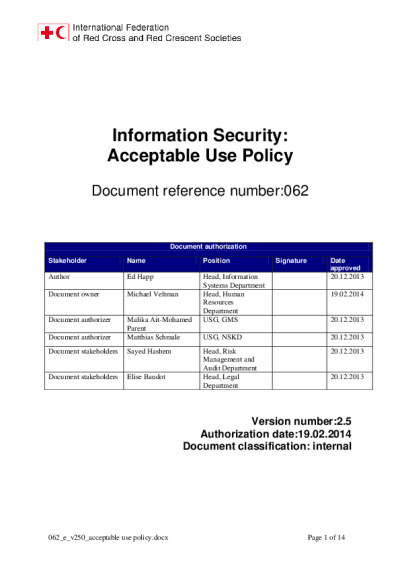
![PDF] Aligning the information security policy with the strategic information systems plan | Semantic Scholar PDF] Aligning the information security policy with the strategic information systems plan | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/b0c460c4ed37b25b46ddb0d855e94683230ecf34/10-Figure1-1.png)
PDF] Aligning the information security policy with the strategic information systems plan | Semantic Scholar