U.S. review finds directed radio frequency attack likely culprit in diplomats' illnesses in Cuba | National Post

Radio Frequency: An Airbone Threat to Corporate and Government Networks | 2020-07-06 | Security Magazine
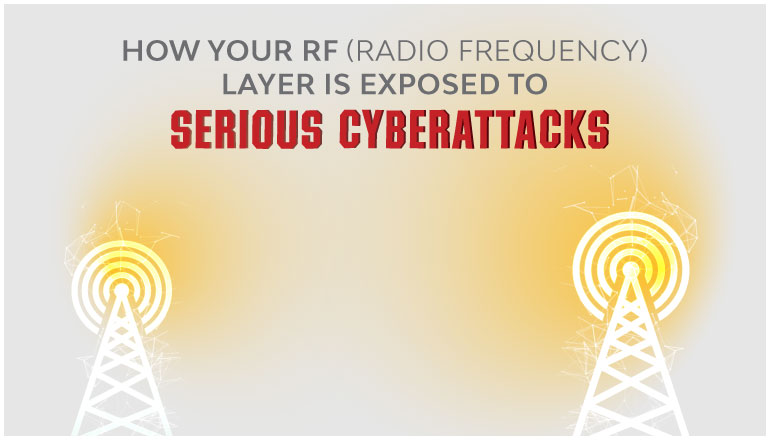
Vecteur Stock Cardiac catheter ablation treatment Atrial fibrillation rhythm problem minimally invasive procedure attack cath lab treat Coronary x-ray Radio frequency Sinus Ventricular SVT ECG ICD Radiofrequency AV | Adobe Stock
Radio Frequency Operations and Training From a Virtually Different Point of View - United States Cybersecurity Magazine
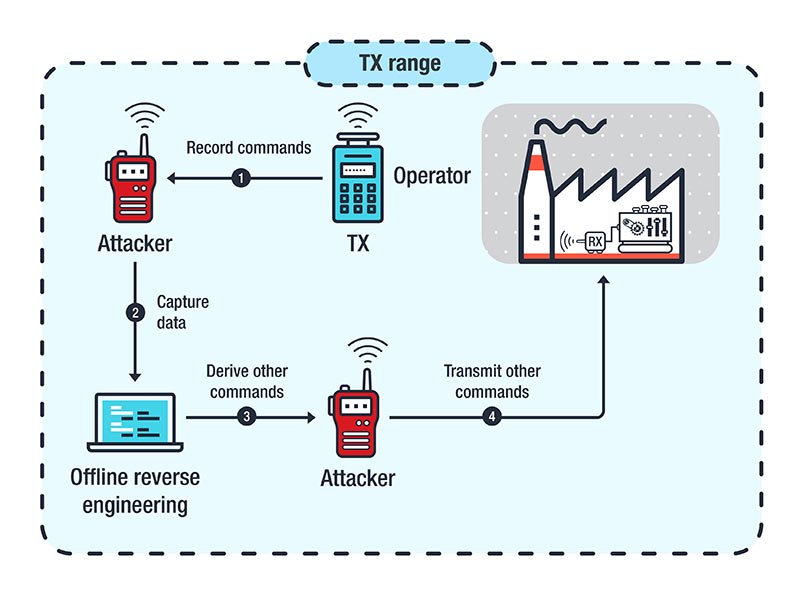
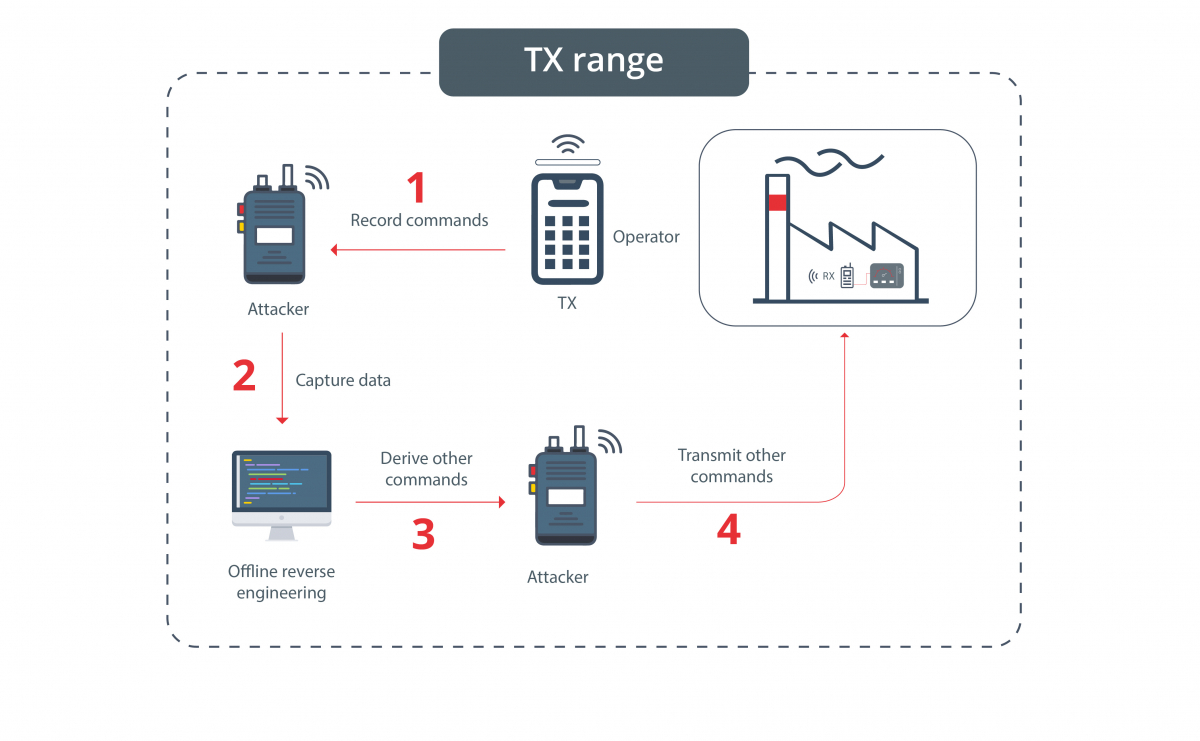
Attacks Against Industrial Machines via Vulnerable Radio Remote Controllers: Security Analysis and Recommendations - Security News





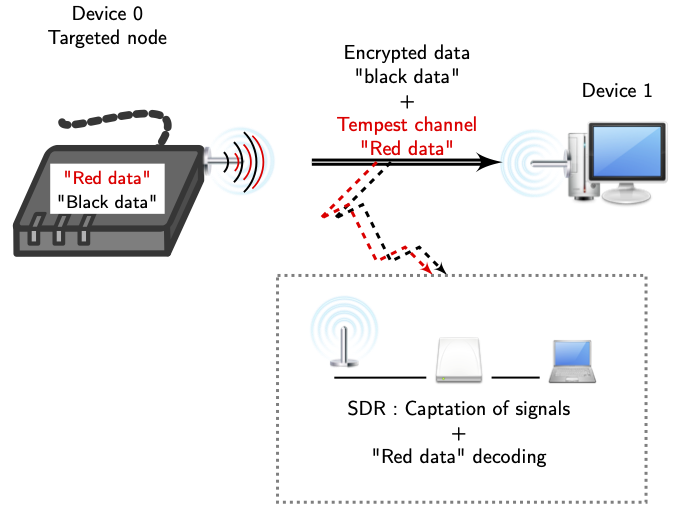
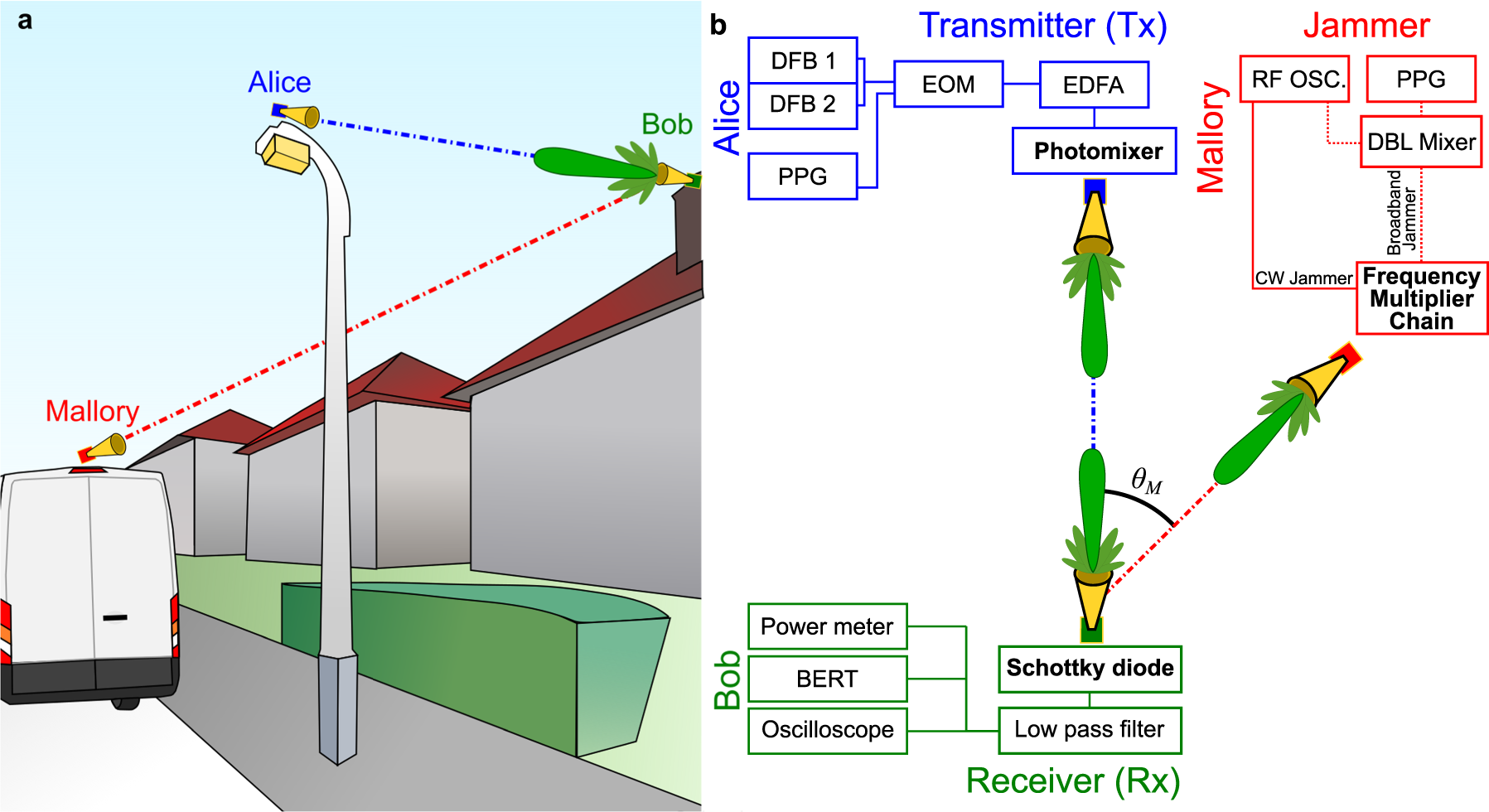
![PDF] A Feasibility Study of Radio-frequency Retroreflector Attack | Semantic Scholar PDF] A Feasibility Study of Radio-frequency Retroreflector Attack | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/b64cba7e85681d499801edc80460d0966c79ffcd/2-Figure1-1.png)
_637280703542341277.png)